You're viewing Apigee Edge documentation.
Go to the
Apigee X documentation. info
When you call an API proxy on Apigee Edge that has OAuth security, Edge is responsible for verifying access tokens. Think of Edge as the gatekeeper -- no API call can pass through that does not have an access token that can be verified.
Adding a VerifyAccessToken policy
To configure token verification, place an OAuthV2 policy with the VerifyAccessToken operation at the very beginning of the API proxy flow (the beginning of the ProxyEndpoint Preflow). If placed there, access tokens will be verified before any other processing takes place, and if a token is rejected, Edge stops processing and returns an error back to the client.
Access the API proxies page, as described below.
Edge
To access the API proxies page using the Edge UI:
- Sign in to apigee.com/edge.
- Select Develop > API Proxies in the left navigation bar.
Classic Edge (Private Cloud)
To access the API proxies page using the Classic Edge UI:
- Sign in to
http://ms-ip:9000, where ms-ip is the IP address or DNS name of the Management Server node. - Select APIs > API Proxies in the top navigation bar.
- From the list, select the proxy you wish to protect.
- In the overview page, click the Develop tab.
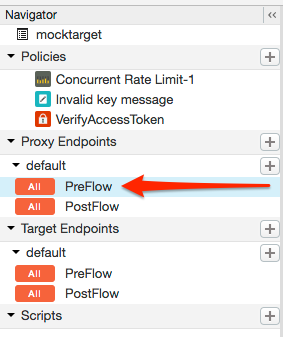
- In the Navigator, select PreFlow for an endpoint listed under Proxy
Endpoints. Typically, the endpoint you want is called "default", although it is possible to
create multiple proxy endpoints. If you do have multiple endpoints, you will probably want to
follow these steps to perform token verification on each one.
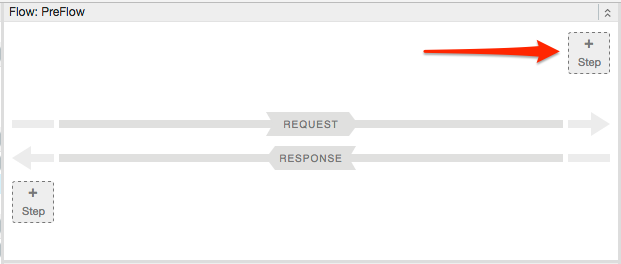
- In the proxy flow editor, click + Step.
- Select Policy Instance New.
- From the policy list, select OAuth v2.0.
- Optionally, change the policy name and display name. For example, for better readability, you might change the display name and name both to "VerifyAccessToken".
- Click Add.
The default policy is already configured with the VerifyAccessToken operation, so you do not have to do anything further:
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<OAuthV2 async="false" continueOnError="false" enabled="true" name="OAuth-v20-1">
<DisplayName>OAuth v2.0 1</DisplayName>
<FaultRules/>
<Properties/>
<Attributes/>
<ExternalAuthorization>false</ExternalAuthorization>
<Operation>VerifyAccessToken</Operation>
<SupportedGrantTypes/>
<GenerateResponse enabled="true"/>
<Tokens/>
</OAuthV2>