Estás viendo la documentación de Apigee Edge.
Ve a la
documentación de Apigee X. info
Consulta este tema para obtener una introducción a la consola de Apigee Sense. En la consola, puedes ver los resultados del análisis de Apigee Sense del tráfico a tus proxies de API. Cuando identifiques clientes que realizan solicitudes sospechosas, como en un ataque de bot, puedes usar la consola para tomar medidas, como bloquear o marcar las solicitudes de la dirección IP de ese cliente.
Como se describe en ¿Qué es Apigee Sense?, Apigee Sense recopila y analiza datos sobre las solicitudes a tus APIs. A través de este análisis, Apigee Sense identifica patrones que podrían representar solicitudes sospechosas. Con la consola de Apigee Sense, puedes ver los resultados del análisis de solicitudes y tomar medidas en función de ellos.
- Abre la Nueva experiencia de Edge.
En la nueva experiencia de Edge, haz clic en el menú Analizar y, luego, en Sensor.
En la página Sense, verás un resumen gráfico de la actividad de solicitudes, incluidas las solicitudes sospechosas.
En la esquina superior derecha de la consola, selecciona la organización de Apigee Edge para la que deseas ver los datos de solicitudes.
Esta es la organización que contiene los proxies de API para los que Apigee Sense recopila datos de solicitudes.
En la esquina superior izquierda, selecciona una fecha para la que tengas datos de análisis de Apigee Sense.
Si seleccionas una fecha, los gráficos de esta página proporcionan una descripción general de alto nivel del análisis de Apigee Sense, incluido el tráfico de solicitudes.

Cómo ver el resumen del análisis de solicitudes
Puedes obtener una vista de alto nivel de la actividad sospechosa. De esta manera, puedes desglosar los datos para obtener más detalles.
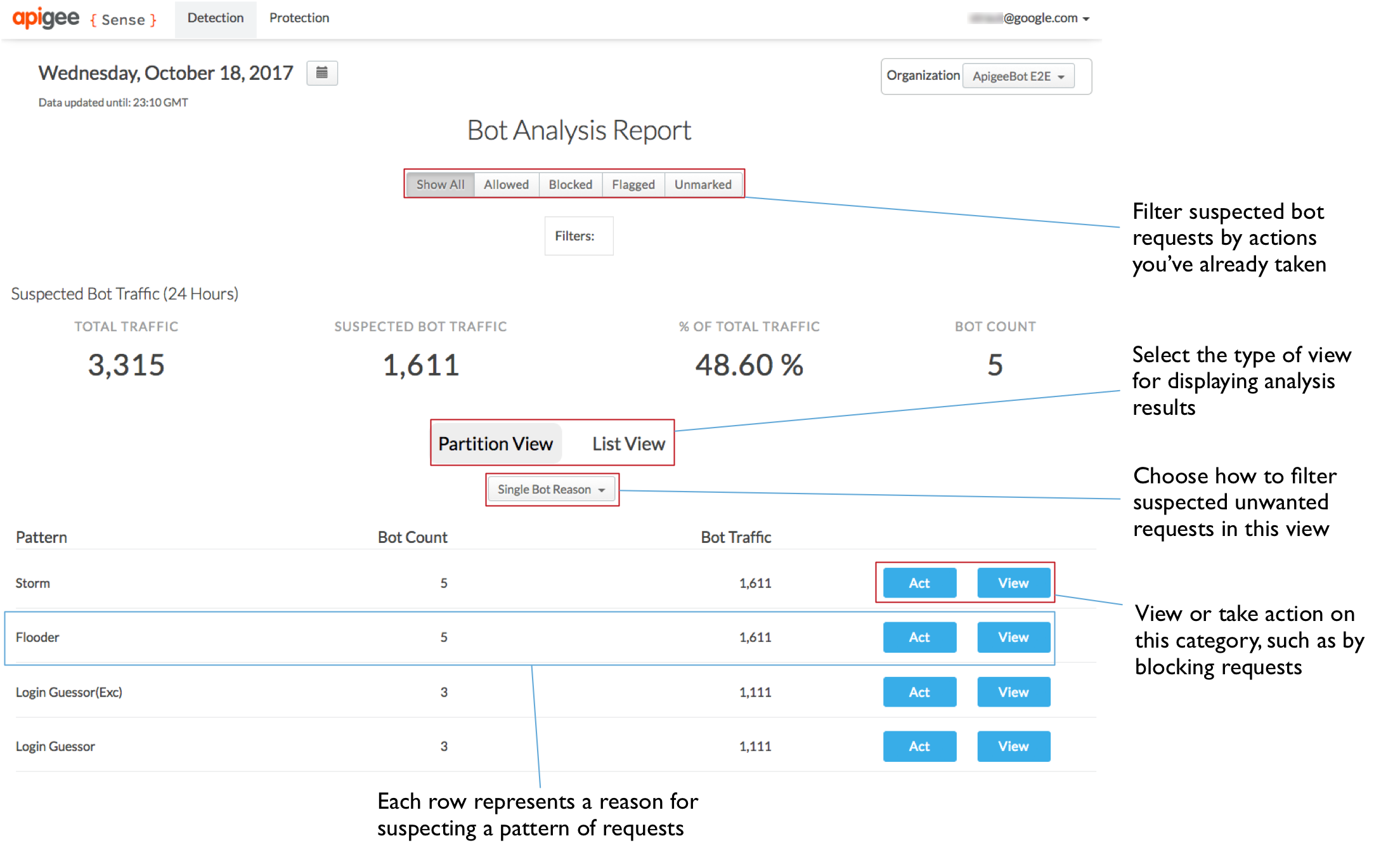
En la parte superior de la página, haz clic en el menú Detección > Informe para ver datos sobre la actividad sospechosa que se encontró entre las solicitudes.
En la página Informe de análisis de bots, la sección Tráfico de bots sospechoso en la parte superior resume el tráfico, con mediciones específicas para las solicitudes sospechosas.
La página Detección también proporciona dos vistas de la actividad sospechosa.
- La vista de particiones agrupa a los clientes por el motivo por el que Apigee Sense los presenta como sospechosos.
- En la vista de lista, se enumeran los clientes de solicitud por su dirección IP, junto con varios otros aspectos de los datos.
En la Vista de particiones, puedes ver el tráfico categorizado en patrones que representan actividad sospechosa. Para obtener más información sobre los patrones, consulta Cómo tomar medidas respecto de actividades sospechosas. El tráfico de solicitudes agrupado en estos patrones es un producto del análisis de tus datos de solicitudes por parte de Apigee Sense.
No todas las solicitudes que cumplen con un patrón son abusivas. Buscas un recuento de bots o números de tráfico muy altos.
Por ejemplo, el patrón Login Attempter representa una gran cantidad de intentos de acceso a un proxy de acceso en un período de 24 horas. En la siguiente imagen, un número muy alto de Bot Count (en relación con otros patrones) indica que una gran cantidad de clientes intentan, en un solo día, conectarse al proxy de acceso. Por lo tanto, vale la pena investigar este patrón.
Cómo investigar con los detalles del análisis
Una vez que hayas identificado un conjunto de solicitudes que podrían incluir actividad sospechosa, como un ataque de bot, puedes obtener una vista más detallada de las solicitudes. Para aislar los ataques de bots genuinos, deberás combinar el análisis de Apigee Sense con tu propio conocimiento de los clientes que llaman a tus APIs.
En la Vista de particiones de la página Detección, busca un patrón que te interese, como uno con un recuento de bots muy alto, y haz clic en el botón Ver para ver los detalles sobre lo que representa el patrón.
Aquí, tienes una vista desglosada de la actividad que se ajusta al patrón que seleccionaste. Hay algunos datos importantes de la lista que se muestra a continuación:
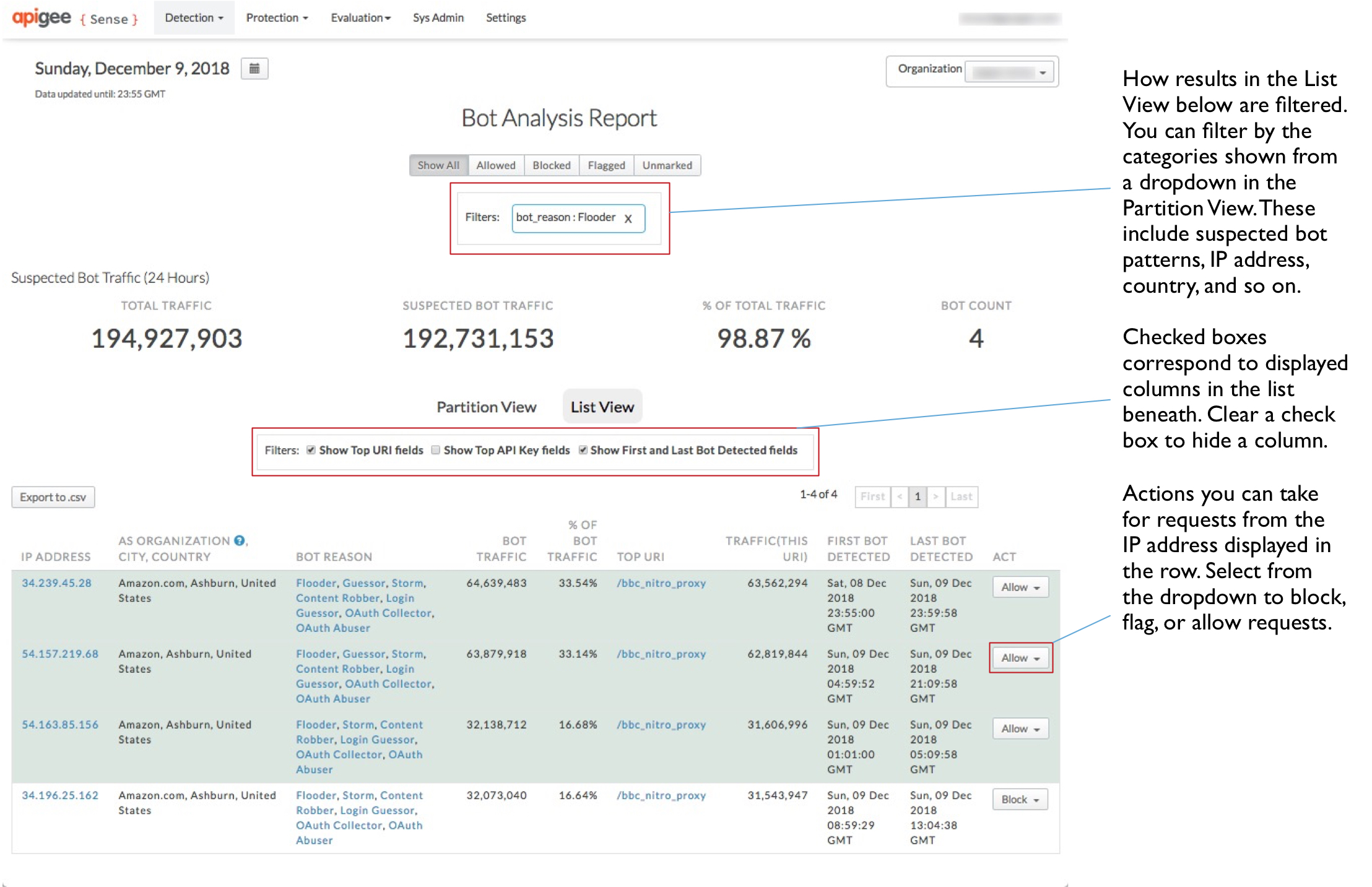
- Hay una gran cantidad de direcciones IP, casi mil en 24 horas.
- Hay una cantidad relativamente pequeña de organizaciones de sistema autónomo (AS) detrás de esas IP, y las organizaciones de AS están distribuidas de forma amplia geográficamente.
- El recuento de tráfico de bots es bastante coherente, entre 250 y 260 en cada IP. Esto también se representa en la medición del % de tráfico de bots.
En conjunto, esta información sugiere que las solicitudes de estas IP representan un ataque coordinado y mecanizado al URI de acceso.
Para ver aún más detalles sobre un solo cliente, haz clic en una de las direcciones IP de la columna izquierda.
Haz clic en la pestaña Detección para ver lo que Apigee Sense descubrió sobre las solicitudes de la dirección IP.
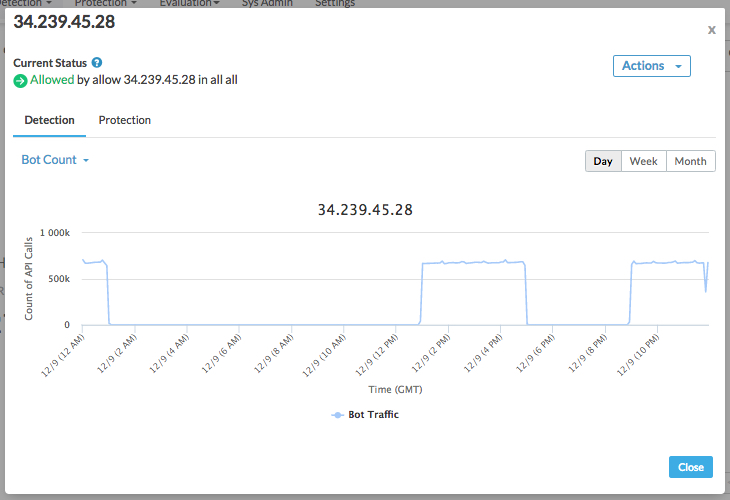
En la parte superior del diálogo, verás una lista de los comportamientos que detectó Apigee Sense para las solicitudes de esta dirección IP.
En Detección, usa las categorías del menú desplegable para decidir si Apigee Edge debe controlar de forma diferente las solicitudes que provienen de una dirección IP. Por ejemplo, las siguientes categorías de valores pueden ayudarte a determinar si la dirección IP representa un ataque:
- Código de estado de la respuesta. Una lista dominada por una gran cantidad de códigos de error, como 500, sugiere que un cliente intenta realizar la solicitud incorrecta de forma reiterada. En otras palabras, un cliente que simplemente envía la solicitud de forma reiterada sin darse cuenta de un resultado de error.
- URI de solicitud: Algunos URI son especialmente significativos como puntos de ataque. Uno de ellos es un URI de acceso.
Haz clic en la pestaña Protección para ver una lista de las reglas de protección que ya se habilitaron para las solicitudes de esta dirección IP.
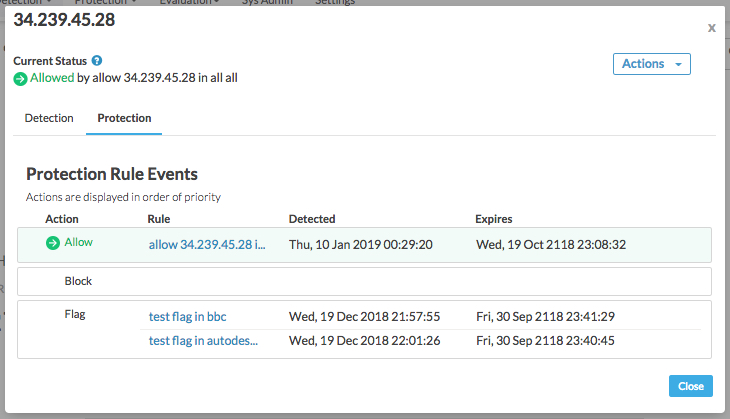
Las reglas se enumeran en orden de prioridad, con la acción de prioridad más alta (Permitir) en la parte superior y la más baja (Marcar) en la parte inferior. En Apigee Sense, puedes realizar varios tipos de acciones en una sola dirección IP. Por lo general, esto se debe a que estás tomando medidas sobre un comportamiento que incluye varias direcciones IP, como para bloquear descifradores de fuerza bruta. Sin embargo, algunas direcciones IP pueden adaptarse a patrones de comportamiento no deseados, como el ataque de descifrado de contraseñas, pero seguir siendo IPs amigables, por ejemplo, cuando tú o un socio prueban el sistema. En ese caso, permitirías esas direcciones IP específicas, independientemente de su comportamiento. Por lo tanto, aunque se habilitarían las acciones de los tres tipos para la dirección IP, la acción Permitir tendría prioridad sobre una acción de Bloquear o Marcar.
Una vez que hayas confirmado que una IP probablemente represente a un cliente sobre el que deseas tomar medidas, puedes interceptar las solicitudes de ese cliente.
En la Vista detallada, haz clic en el botón Cerrar.
Toma medidas con respecto a los clientes que realizan solicitudes sospechosas
¿Tienes la certeza de que tienes un cliente cuyas solicitudes quieres interceptar, como un ataque de bot? Compón una regla para bloquear o marcar las solicitudes del cliente antes de que lleguen a tus proxies.
En la página Detección, en el Informe de análisis de bots, haz clic en la pestaña Vista de partición para volver a ver la lista de patrones.
En la Vista de particiones, observa que la lista de patrones se acortó para incluir solo el que seleccionaste para ver antes. Esto se debe a que, cuando seleccionaste ver el patrón, comenzaste a filtrar la lista completa de resultados solo para ese patrón. Los patrones por los que filtras se muestran en el cuadro Filtros, cerca de la parte superior de la página.
En la fila del patrón, haz clic en el botón Act para especificar una acción que se realizará para las solicitudes de IP que coincidan con el patrón.
En el cuadro de diálogo Compose Rule, define cómo Apigee Edge responderá a las solicitudes de las IP que realicen llamadas en el patrón que seleccionaste.
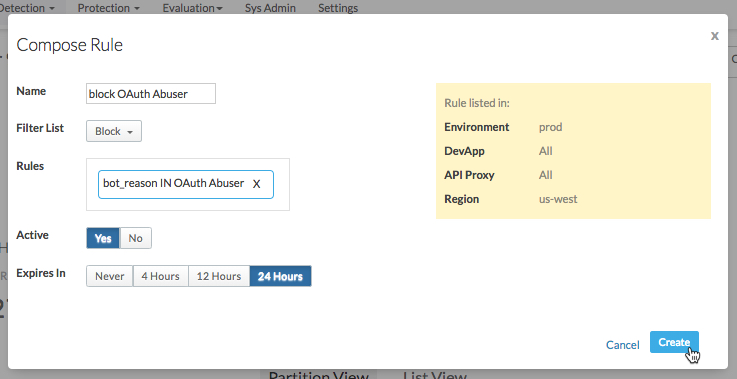
Aquí, especificarás una regla que usa Apigee Edge cuando se reciben solicitudes de una IP en el patrón.
- Ingresa un nombre para la regla nueva, como
Block login attempters. En la Lista de filtros, selecciona la acción que deseas que realice Apigee Edge:
- Permite que la solicitud se envíe a tu proxy como antes.
- Bloquea la solicitud por completo antes de que el proxy comience a procesarla.
- Para marcar la solicitud, haz que Apigee Edge agregue un encabezado HTTP especial que tu proxy pueda buscar. Apigee Edge agregará un encabezado
X-SENSE-BOT-DETECTEDcon un valor deSENSE. Por ejemplo, te recomendamos que configures tu proxy para que, cuando recibas una solicitud de un cliente en particular, puedas enviarle datos simulados para engañarlo. En tu proxy, examinarías los encabezados de las solicitudes entrantes y, luego, responderías de manera adecuada cuando se reciba una solicitud marcada.
En el cuadro Rules, confirma que las reglas que se muestran sean las que deseas que Apigee Sense use cuando crees la regla.
En Activa, selecciona Sí para activar la regla.
Selecciona un período después del cual deseas que venza la regla (para que Apigee Edge deje de aplicarla).
- Ingresa un nombre para la regla nueva, como
Haz clic en Crear para enviar la regla a Apigee Edge.
Revisa las reglas que creaste
Si tomaste medidas para implementar reglas para responder a ciertos clientes, puedes administrarlas en la página Reglas de protección.
- En la parte superior de la página, haz clic en el menú Protección > Reglas para ver una lista de las reglas que tienes implementadas.
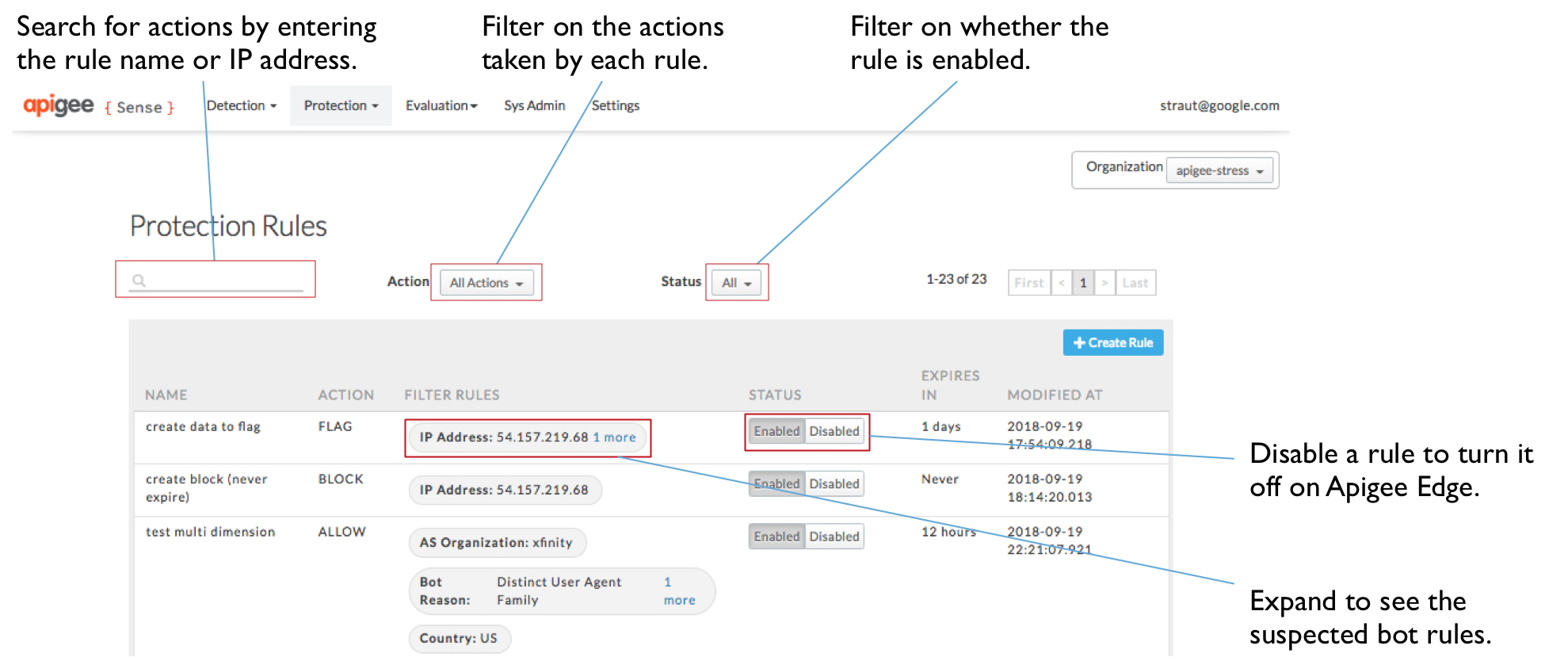
- En la página Protection Rules, puedes ver la lista de reglas que creaste. Desde allí, puedes hacer lo siguiente:
- Ingresa un valor en el cuadro de búsqueda para filtrar las reglas por valores de la lista, como el nombre o la dirección IP.
- Consulta los detalles de una regla o averigua en qué IPs estás tomando medidas.
- Haz clic en un valor de la columna Filtros para ver qué compone la regla.
- Habilita o inhabilita reglas.

