The SAML specification defines three entities:
- Principal (Edge UI user)
- Service provider (Apigee SSO)
- Identity provider (returns a SAML assertion)
When SAML is enabled, the principal (an Edge UI user) requests access to the service provider (Apigee SSO). Apigee SSO (in its role as a SAML service provider) then requests and obtains an identity assertion from the SAML IDP and uses that assertion to create the OAuth2 token required to access the Edge UI. The user is then redirected to the Edge UI.
This process is shown below:
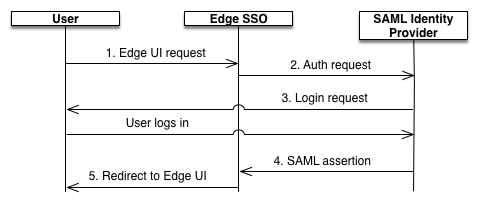
In this diagram:
- The user attempts to access the Edge UI by making a request to the login URL for the Edge
UI. For example:
https://edge_UI_IP_DNS:9000 - Unauthenticated requests are redirected to the SAML IDP. For example, "https://idp.customer.com".
- If you are not logged in to the IDP, you are prompted to log in.
You are authenticated by the SAML IDP.
The SAML IDP generates and returns a SAML 2.0 assertion to the Apigee SSO module.
- Apigee SSO validates the assertion, extracts the user identity from the assertion, generates
the OAuth 2 authentication token for the Edge UI, and redirects the user to the main Edge UI
page at the following URL:
https://edge_ui_IP_DNS:9000/platform/orgName
Where orgName is the name of an Edge organization.
