The SAML specification defines three entities:
- Principal (Edge UI user)
- Service provider (Apigee SSO)
- Identity provider (returns SAML assertion)
When SAML is enabled, the principal (an Edge UI user) requests access to the service provider (Apigee SSO). Apigee SSO (in its role as a SAML service provider) then requests and obtains an identity assertion from the SAML IDP and uses that assertion to create the OAuth2 token required to access the Edge UI. The user is then redirected to the Edge UI.
This process is shown below:
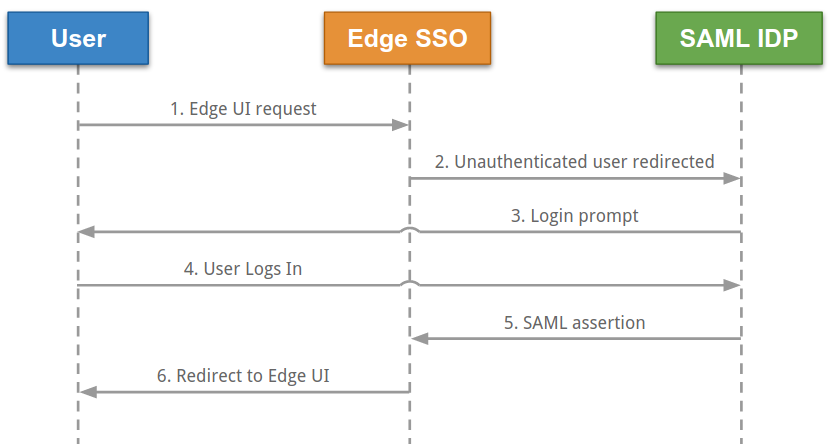
In this diagram:
- The user attempts to access the Edge UI by making a request to the login URL for the Edge
UI. For example:
https://edge_ui_IP_DNS:9000 - Unauthenticated requests are redirected to the SAML IDP. For example, "https://idp.customer.com".
- If the user is not logged in to the identity provider, then they are prompted to log in.
- The user logs in.
- The user is authenticated by the SAML IDP, which generates a SAML 2.0 assertion and returns it to the Apigee SSO.
- Apigee SSO validates the assertion, extracts the user identity from the assertion, generates
the OAuth 2 authentication token for the Edge UI, and redirects the user to the main Edge UI
page at:
https://edge_ui_IP_DNS:9000/platform/orgName
Where orgName is the name of an Edge organization.
Edge supports many IDPs, including Okta and the Microsoft Active Directory Federation Services (ADFS). For information on configuring ADFS for use with Edge, see Configuring Edge as a Relying Party in ADFS IDP. For Okta, see the following section.
To configure your SAML IDP, Edge requires an email address to identify the user. Therefore, the identity provider must return an email address as part of the identity assertion.
In addition, you might require some or all of the following:
| Setting | Description |
|---|---|
| Metadata URL |
The SAML IDP might require the metadata URL of Apigee SSO. The metadata URL is in the form: protocol://apigee_sso_IP_DNS:port/saml/metadata For example: http://apigee_sso_IP_or_DNS:9099/saml/metadata |
| Assertion Consumer Service URL |
Can be used as the redirect URL back to Edge after the user enters their IDP credentials, in the form: protocol://apigee_sso_IP_DNS:port/saml/SSO/alias/apigee-saml-login-opdk For example: http://apigee_sso_IP_or_DNS:9099/saml/SSO/alias/apigee-saml-login-opdk |
|
Single logout URL |
You can configure Apigee SSO to support single logout. See Configure single sign-out from the Edge UI for more. The Apigee SSO single logout URL has the form: protocol://apigee_SSO_IP_DNS:port/saml/SingleLogout/alias/apigee-saml-login-opdk For example: http://1.2.3.4:9099/saml/SingleLogout/alias/apigee-saml-login-opdk |
|
The SP entity ID (or Audience URI) |
For Apigee SSO: apigee-saml-login-opdk |
Configuring Okta
To configure Okta:
- Log in to Okta.
- Select Applications and then select your SAML application.
- Select the Assignments tab to add any users to the application. These user will be able to log in to the Edge UI and make Edge API calls. However, you must first add each user to an Edge organization and specify the user's role. See Register new Edge users for more.
- Select the Sign on tab to obtain the Identity Provider metadata URL. Store that URL because you need it to configure Edge.
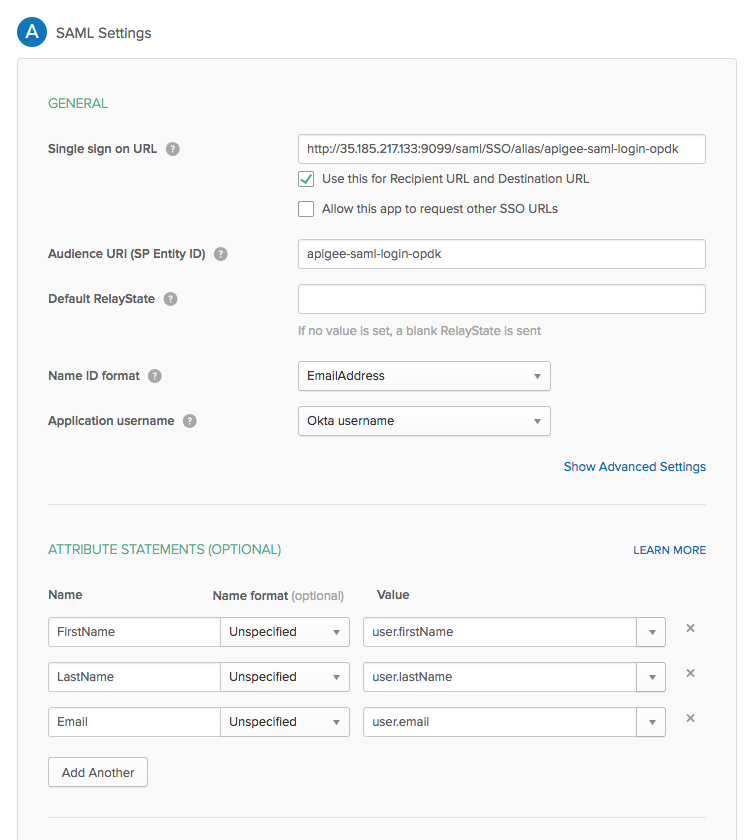
- Select the General tab to configure the Okta application, as shown in the
table below:
Setting Description Single sign on URL Specifies the redirect URL back to Edge for use after the user enters their Okta credentials. This URL is in the form: http://apigee_sso_IP_DNS:9099/saml/SSO/alias/apigee-saml-login-opdk
If you plan to enable TLS on
apigee-sso:https://apigee_sso_IP_DNS:9099/saml/SSO/alias/apigee-saml-login-opdk
Where apigee_sso_IP_DNS is the IP address or DNS name of the node hosting
apigee-sso.Note that this URL is case sensitive and SSO must appear in caps.
If you have a load balancer in front to
apigee-sso,then specify the IP address or DNS name ofapigee-ssoas referenced through the load balancer.Use this for Recipient URL and Destination URL Set this checkbox. Audience URI (SP Entity ID) Set to apigee-saml-login-opdkDefault RelayState Can leave blank. Name ID format Specify EmailAddress.Application username Specify Okta username.Attribute Statements (Optional) Specify FirstName,LastName, andEmailas shown in the image below.
The SAML settings dialog box should appear as below once you are done: