Private Cloud v4.18.01 專用 Edge
Edge UI 和 Edge Management API 的運作方法是向 Edge Management Server 提出要求。 管理伺服器支援下列類型的驗證:
- 基本驗證:登入 Edge UI 或向 Edge 管理提出要求 API,以便傳送您的使用者名稱和密碼。
- OAuth2 交換您的 Edge 基本驗證憑證以取得 OAuth2 存取權 權杖和重新整理權杖傳遞 OAuth2 存取權,呼叫 Edge Management API 傳遞到 API 呼叫的 Bearer 標頭中。
Edge 也支援以安全宣告標記語言 (SAML) 2.0 做為驗證方式 以注意力機制為基礎啟用 SAML 後,Edge UI 和 Edge Management API 的存取權仍會使用 OAuth2 存取權杖不過,現在您可以由 SAML 傳回的 SAML 宣告產生這些符記 識別資訊提供者
注意:SAML 僅支援驗證機制。不 可支援授權。因此,您還是能使用 Edge OpenLDAP 資料庫來維護 授權資訊。請參閱指派角色,瞭解 內容。
SAML 支援單一登入 (SSO) 環境。使用 SAML 搭配 Edge 即可支援單一登入 (SSO) 服務 除了您提供的任何其他服務,也支援 Edge UI 和 API 。
為不公開的 Edge 新增 OAuth2 支援功能 雲朵形
如上所述,SAML 的 Edge 實作需要 OAuth2 存取憑證。因此, Edge for Private Cloud 已新增 OAuth2 支援。詳情請參閱 OAuth 2.0 簡介。
SAML 的優勢
SAML 驗證提供多項優點。使用 SAML 可以:
- 完全掌控使用者。使用者從貴機構離職 集中取消佈建時,系統會自動拒絕存取 Edge。
- 控管使用者通過 Edge 的驗證方式。你可以選擇不同的驗證方法 適合不同的 Edge 機構類型
- 控管驗證政策。您的 SAML 供應商可能支援驗證政策 並且更加符合企業標準
- 您可以監控以下項目的登入、登出、登入失敗和高風險活動: 也就是邊緣部署項目
透過 Edge 使用 SAML
如要在 Edge 上支援 SAML,請安裝 Edge SSO 模組 apigee-sso。 這張圖片顯示 Edge for Private Cloud 安裝項目中的 Edge SSO:
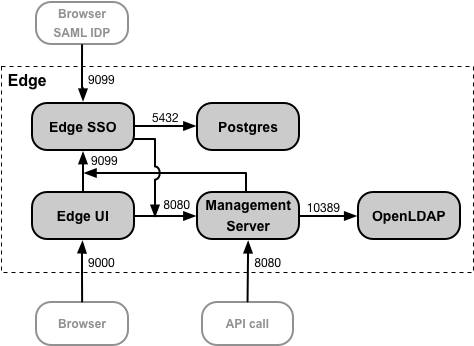
您可以在與 Edge UI 和 Management Server 相同的節點上安裝 Edge 單一登入 (SSO) 模組,或是 自己的節點確認 Edge SSO 可透過通訊埠 8080 存取管理伺服器。
通訊埠 9099 必須在 Edge SSO 節點上開啟,才能透過瀏覽器存取 Edge 單一登入。 ,以及透過「管理伺服器和 Edge UI」輸入外部 SAML IDP。在設定過程中 邊緣單一登入 (SSO) 時,您可以指定外部連線使用 HTTP 或加密 HTTPS 因此效能相當卓越
邊緣單一登入 (SSO) 會使用 Postgres 節點通訊埠 5432 上可存取的 Postgres 資料庫。通常是您 可使用您搭配 Edge 安裝的 Postgres 伺服器 (獨立的 Postgres ) 伺服器或兩部在主要/待命模式下設定的 Postgres 伺服器。如果 Postgres 的負載 伺服器偏高,您也可以選擇建立專門用於 Edge 單一登入 (SSO) 的 Postgres 節點。
啟用 SAML 後,Edge UI 和 Edge Management API 的存取權就會使用 OAuth2 存取權杖。 這些權杖是由 Edge SSO 模組產生,該模組會接受由 您的 IdP。
從 SAML 宣告產生後,OAuth 權杖的有效期限為 30 分鐘,且重新整理 權杖的有效期限為 24 小時。您的開發環境可能支援一般用途的自動化作業 開發任務,例如測試自動化或持續整合/持續部署 (CI/CD),需要較長的權杖使用時間。如要進一步瞭解如何建立專案,請參閱使用 SAML 搭配自動化工作一文 以便處理自動化任務的特殊符記
Edge UI 和 API 網址
用來存取 Edge UI 和 Edge Management API 的網址與先前使用的網址相同 您已啟用 SAML。針對 Edge UI:
http://edge_ui_IP_DNS:9000 https://edge_ui_IP_DNS:9000
其中 edge_ui_IP_DNS 是電腦的 IP 位址或 DNS 名稱 負責託管 Edge UI設定 Edge UI 時,您可以指定連線使用 HTTP 或加密 HTTPS 通訊協定
針對 Edge Management API:
http://ms_IP_DNS:8080/v1 https://ms_IP_DNS:8080/v1
其中 ms_IP_DNS 是管理作業的 IP 位址或 DNS 名稱 伺服器設定 API 時,您可以指定連線使用 HTTP 或 加密 HTTPS 通訊協定
在邊緣單一登入 (SSO) 中設定 TLS
根據預設,連至邊緣單一登入 (SSO) 的連線會使用節點託管的通訊埠 9099 使用 HTTP apigee-sso,Edge 單一登入 (SSO) 模組。 建構於 apigee-sso 是 Tomcat 處理 HTTP 和 HTTPS 要求
Edge SSO 和 Tomcat 支援三種連線模式:
- DEFAULT - 預設設定支援通訊埠上的 HTTP 要求 9099。
- SSL_TERMINATION:已啟用 TLS 對邊緣單一登入 (SSO) 的存取權 就是用哪一種烤箱或刀子都可以 那麼預先建構的容器或許是最佳選擇您必須為這個模式指定 TLS 金鑰和憑證。
- SSL_PROXY:在 Proxy 模式下設定 Edge SSO,表示您已安裝 負載平衡器位於 apigee-sso 之前,並在負載時終止 TLS 。您可以為來自負載的要求,指定在 apigee-sso 使用的通訊埠 。
為 開發人員服務入口網站和 API BaaS
啟用 Edge 的 SAML 支援後,您可以選擇為下列項目啟用 SAML:
- API BaaS:BaaS 入口網站和 BaaS 堆疊均支援使用者的 SAML 驗證。請參閱為 API BaaS 啟用 SAML 內容。
- 開發人員服務入口網站 - 這個入口網站支援 SAML 驗證。 向 Edge 發出要求請注意,這與開發人員的 SAML 驗證不同 登入入口網站針對開發人員登入設定 SAML 驗證。詳情請見 設定 「開發人員服務」入口網站,使用 SAML 與 Edge 通訊,以取得更多資訊。
設定開發人員服務入口網站和 API BaaS 時,您必須指定 您透過 Edge 安裝的 Edge SSO 模組:
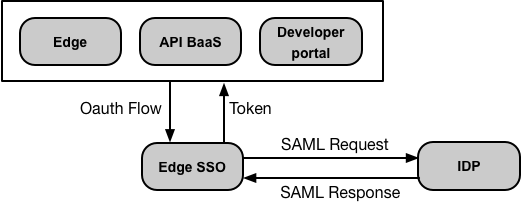
由於 Edge 和 API BaaS 共用相同的 Edge 單一登入 (SSO) 模組,因此支援單一登入。沒錯 請登入 Edge 或 API BaaS 同時登入兩者這也表示,您只需要 所有使用者憑證均須存放在同一個位置。
您也可以選擇設定單一登入。請參閱「從 Edge UI 設定單一登入」。
